
April 15, 2026

On February 2, 2026, the FDA officially retired the Quality System Inspection Technique (QSIT) and began enforcing inspections under the new Quality Management System Regulation (QMSR) Compliance Program Manual 7382.850. For medical device manufacturers, especially those building connected or software-enabled products, this isn't a minor procedural update. It's a fundamental change in how the FDA evaluates quality systems, with cybersecurity now squarely in the enforcement crosshairs.
In a recent webinar, Naomi Schwartz, VP of Regulatory Strategy at MedCrypt, provided a no-filter breakdown of what this transition means in practice, including a recap of 2025's deficiency trends and a forward look at what inspectors will be scrutinizing in 2026 and beyond. Here are the key takeaways every device manufacturer should know.
The old QSIT framework, first published in 1999, was built for an era before connected devices, cloud-based software updates, and sophisticated cyber threats were part of everyday medical technology. It focused primarily on inspection technique and methodology for assessing traditional quality system compliance. Cybersecurity wasn't on the radar because, for most of the device world, it didn't need to be yet.
The new QMSR Compliance Program Manual represents a modernized approach. It incorporates ISO 13485:2016 by reference, aligns U.S. requirements with international standards, and most significantly for our purposes, it explicitly addresses cybersecurity requirements and enforcement. The manual includes specific guidance for evaluating "cyber devices" under Section 524B of the FD&C Act and provides new statutory and regulatory requirements that simply didn't exist when QSIT was developed.
Understanding the distinction between these two frameworks is essential for planning your compliance strategy. The differences extend well beyond naming conventions.

One of the most operationally significant changes is the removal of the previous exemption for internal audit and management review records. Under QSIT, those records were off limits to inspectors. Under QMSR, the FDA can and will examine them. This means your management team's engagement with cybersecurity risk, or lack thereof, is now visible during an inspection.
The QMSR introduces two distinct inspection models that apply to different situations. Both cover core QMS areas, but they differ significantly in scope.
Model 1 applies to at minimum one element from each QMS area. Think of it as a sampling approach. Model 2 is far more extensive, covering all elements in each area at minimum. Both models also include general items such as registration and listing, marketing authorizations, and follow-up on previous 483 observations.
The practical implication: if your facility is selected for a Model 2 inspection, the investigator is going deep. Having a single strong area won't compensate for weaknesses elsewhere.
Section 524B is where the enforcement teeth are. The QMSR Compliance Program Manual defines "cyber devices" under Section 524B(c) as devices that include software, have the ability to connect to the internet (intentionally or unintentionally), and contain technological characteristics that could be vulnerable to cybersecurity threats.
For devices submitted after March 29, 2023, the requirements are clear and enforceable. Manufacturers must comply with Section 524B(b)(2), and failure to do so is classified as a prohibited act under Section 301(q) of the FD&C Act. This isn't a guidance document recommendation. It carries the force of law.
The Grandfathering Nuance: Devices submitted before March 29, 2023, are technically exempt from 524B requirements. However, they must still comply with state-of-the-art design standards. Under Section 518(b), the FDA retains authority to order repairs, replacements, or refunds for devices that present an unreasonable risk of substantial harm to public health. The costly Philips Respironics recall is a cautionary example of what happens when legacy devices fall behind current design expectations.
The FDA has included a dedicated cybersecurity section in the QMSR Compliance Program Manual, a strong signal that cybersecurity elements will receive the same level of inspector attention as traditional areas like Other Applicable FDA Requirements (OAFRs), Registration & Listing issues, and specialty areas such as radiation-emitting devices.
Inspectors will be evaluating several key areas:
Design History FilesHow well does your DHF demonstrate that you follow your own cybersecurity procedures? If your QMS includes formalized cybersecurity processes but your DHF shows gaps in execution, that creates nonconformances and CAPAs, which become evidence of systemic issues.
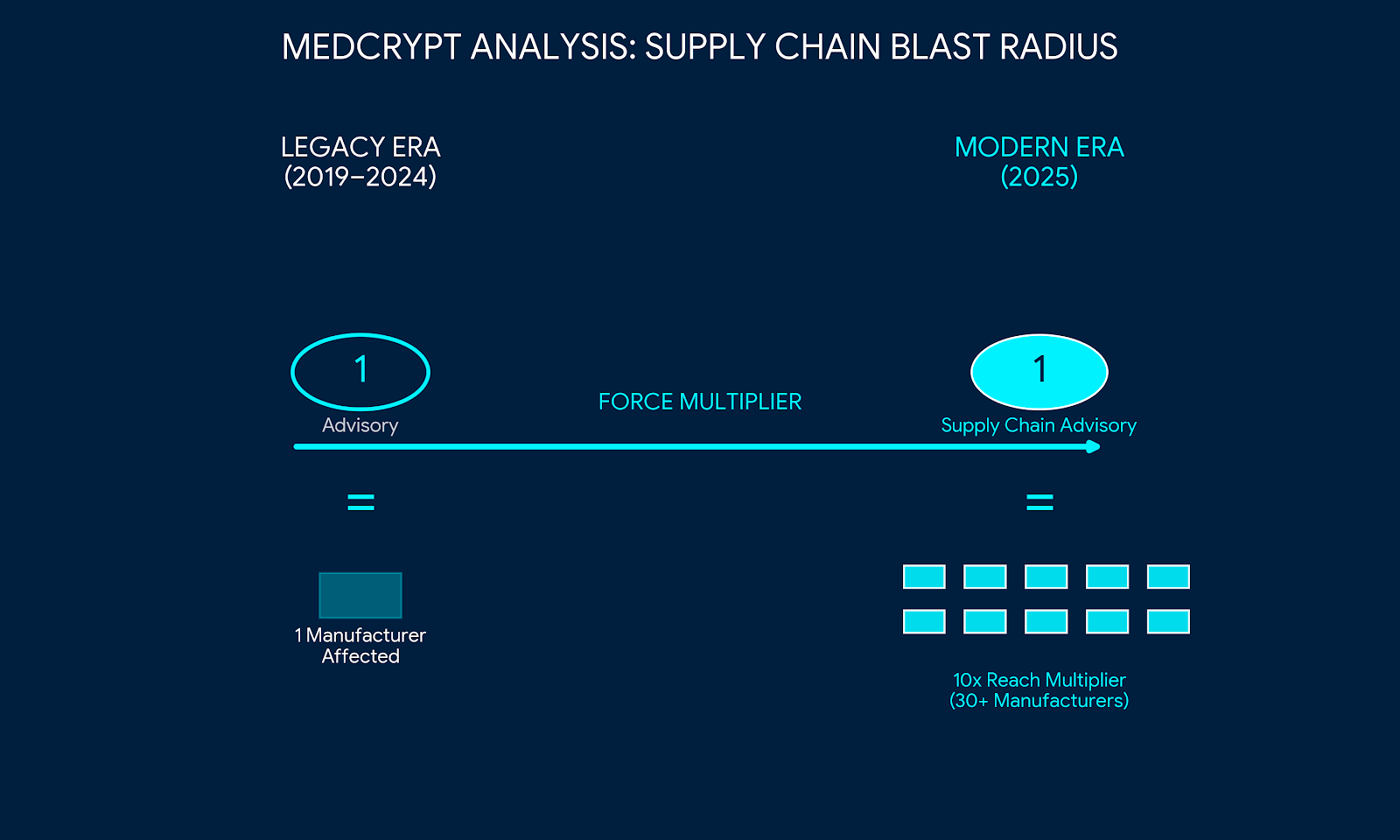
Software Bill of Materials (SBOMs)SBOMs are now explicitly required for cyber devices under Section 524B(b)(3). They must track your software supply chain comprehensively and be maintained as a living document.
Vulnerability ManagementReal-time monitoring and tracking of vulnerabilities, with documented evidence of how security gaps are identified, assessed, and resolved throughout the device lifecycle.
Incident Response PlansComprehensive plans that outline steps to mitigate potential breaches and ensure rapid recovery, demonstrating organizational readiness rather than aspirational documentation.
Management Review RecordsWith the previous exemption removed, inspectors can now see whether leadership is actively engaged in understanding cybersecurity risks and investing in mitigation. Passive awareness won't suffice.
The QMSR Compliance Program Manual outlines two primary situations that determine how inspection findings are classified.
When inspectional findings reveal serious, systemic, or repeat deviations from the regulation, and there's evidence of adverse impact or significant risk to patients and users, the inspection will be classified as OAI. This can lead to Warning Letters, consent decrees, or Department of Justice referrals. Inspectors are specifically instructed to pay attention to the relationships between requirements, meaning a pattern of deficiencies across multiple QMS areas compounds the severity.
Less significant deviations with minimal or no public health impact typically result in a VAI classification. In these cases, the Form FDA-483 observations serve as notice, and the manufacturer is expected to take voluntary corrective action.
Beyond routine surveillance inspections, manufacturers should be aware that directed inspections are often initiated by whistleblower complaints or post-market signals. The FDA gathers evidence incrementally without revealing the source of the complaint, and inspectors maintain strict confidentiality regarding whistleblower identities. Companies should operate under the assumption that any internal compliance gaps could surface through this channel.
The FDA's updated requirements are also influencing the international regulatory landscape. BSI and other Notified Bodies are increasingly adopting cybersecurity-focused audit approaches that align with QMSR expectations. For manufacturers operating across multiple jurisdictions, including under MDSAP, this means cybersecurity compliance is becoming a universal market-access requirement rather than a U.S.-specific obligation.
The trend lines are clear. The FDA is moving toward more enforcement, more remote regulatory assessments, and deeper scrutiny of cybersecurity-related documentation. Manufacturers who treat cybersecurity as a checkbox exercise will find themselves on the wrong side of an inspection finding.
Practical steps to take now: ensure your design history files clearly tie back to your cybersecurity processes; verify that any procedures formalized in your QMS can actually be followed as written; update your internal audit program to include cybersecurity conformity as a standing area of review; train auditors to evaluate cybersecurity risk management with the same rigor as any other QMS element; and make sure management review records reflect active, informed engagement with cybersecurity issues.
MedCrypt helps medical device manufacturers navigate cybersecurity compliance, from pre-market submissions through post-market surveillance. Don't wait for an inspection finding to take action.

May 28, 2026
March 12, 2026

March 4, 2026
Get the latest healthcare cybersecurity news right in your inbox.
We'll never spam you or sell your information

