February 27, 2026

There was a time when "cybersecurity" was a line item buried in the IT budget of a medical device company—a technical hurdle to be cleared once and then managed in the background or something to address later and if a problem arises. That time is officially over.
In the last year, a quiet but massive shift has occurred in how the FDA, SEC, and DOJ view connected devices. We’re seeing a new brand of enforcement: one where security isn't just about patient safety. In addition to regulatory drivers, shareholder value, market timing, and federal fraud all playing into enforcement. If you’re a MedTech executive, here is the new reality of the regulatory landscape and how to keep your next launch from becoming a cautionary tale.
Historically, if your device safely performed its clinical function and the clinical trials were sound, you were largely in the clear. Today, the FDA is leveraging its updated statutory cybersecurity powers, mandated under Section 524B to act as a much more aggressive gatekeeper. We are increasingly seeing the agency issue "Refuse to Accept" (RTA) letters or hold up 510(k) clearances not because of a mechanical fault, but due to incomplete or insufficient cybersecurity and supporting documentation.
This isn't just a minor regulatory hiccup. For a medical device manufacturer, losing one to two full quarters of market time while scrambling to retrofit security protocols can be devastating. Beyond the immediate loss of projected revenue, these delays allow competitors to seize market share and can sour relationships with hospital systems that were counting on a specific rollout timeline. In the current climate, a robust security posture is the only way to ensure your product launch stays on schedule and allows a manufacturer to protect market share.
One of the most telling trends of late 2025 is that regulators not only are looking at cybersecurity during the market approval process but we are also seeing recalls or corrective action for fielded devices because of cybersecurity reasons. Meaning, manufacturers are expected to monitor their devices' cybersecurity posture in the postmarket and are expected to address high risk vulnerabilities through the appropriate regulatory pathways.
We are seeing significant fines levied against companies for failing to identify cybersecurity vulnerabilities in fielded devices or for misstating compliance with cybersecurity standards, i.e., they failed in their premarket cybersecurity processes as well as in their postmarket cybersecurity risk management obligations. This demonstrates that the federal government no longer views "already passing market approval" as an excuse for being "insecure." If you are still generating revenue from a device designed a decade ago that lacks modern authentication or patching capabilities, you are carrying a massive, unmitigated liability that federal investigators are now actively hunting.
As one example of a government agency taking aggressive action, the Department of Justice has been using the False Claims Act (FCA) to target companies that misrepresent their security posture, insufficiently incorporated cybersecurity practices during software development, or failed to address newly identified cyber risks in fielded systems and devices.
This is where the risk shifts from engineering to the C-suite. The SEC is now treating cybersecurity vulnerabilities as a matter of risk and consequently financial transparency.While a security flaw necessitating a recall or major patch often triggers an immediate 'material impact' on stock price, the long-term narrative depends entirely on execution: recalls are an expected reality of modern engineering, and a manufacturer that communicates with radical transparency and speed can actually bolster its reputation for integrity. The true financial and reputational crisis only emerges when a company obfuscates the truth, acts with negligence, or fails to report the issue, transforming a manageable technical hurdle into a permanent breach of public trust.
Regulators are now scrutinizing the gap between when leadership became aware of a security risk and when they disclosed that risk to their customers and shareholders. If a company continues to project growth while sitting on a known, unaddressed high-risk cyber-vulnerability, they risk being hit with "material omission" charges. The message is clear: leadership can no longer silo security as a technical problem. If it has the potential to impact the bottom line or patient safety, it is a disclosure requirement that must be handled with the same gravity as a financial audit.
As we integrate AI into clinical workflows, we’re entering a complex regulatory "grey area." While the FDA has established high standards for AI-enabled diagnostic tools, there is a notable lack of oversight on certain clinical modalities—specifically generative AI used for clinical documentation, administrative support, or "low-risk" patient triaging.
However, don't mistake a current lack of specific oversight to protect you from future risk. The regulatory posture is rapidly moving toward a Total Product Life Cycle (TPLC) approach. Even if your specific AI modality isn't strictly regulated today, the expectation is that you have a "Predetermined Change Control Plan" (PCCP) in place.
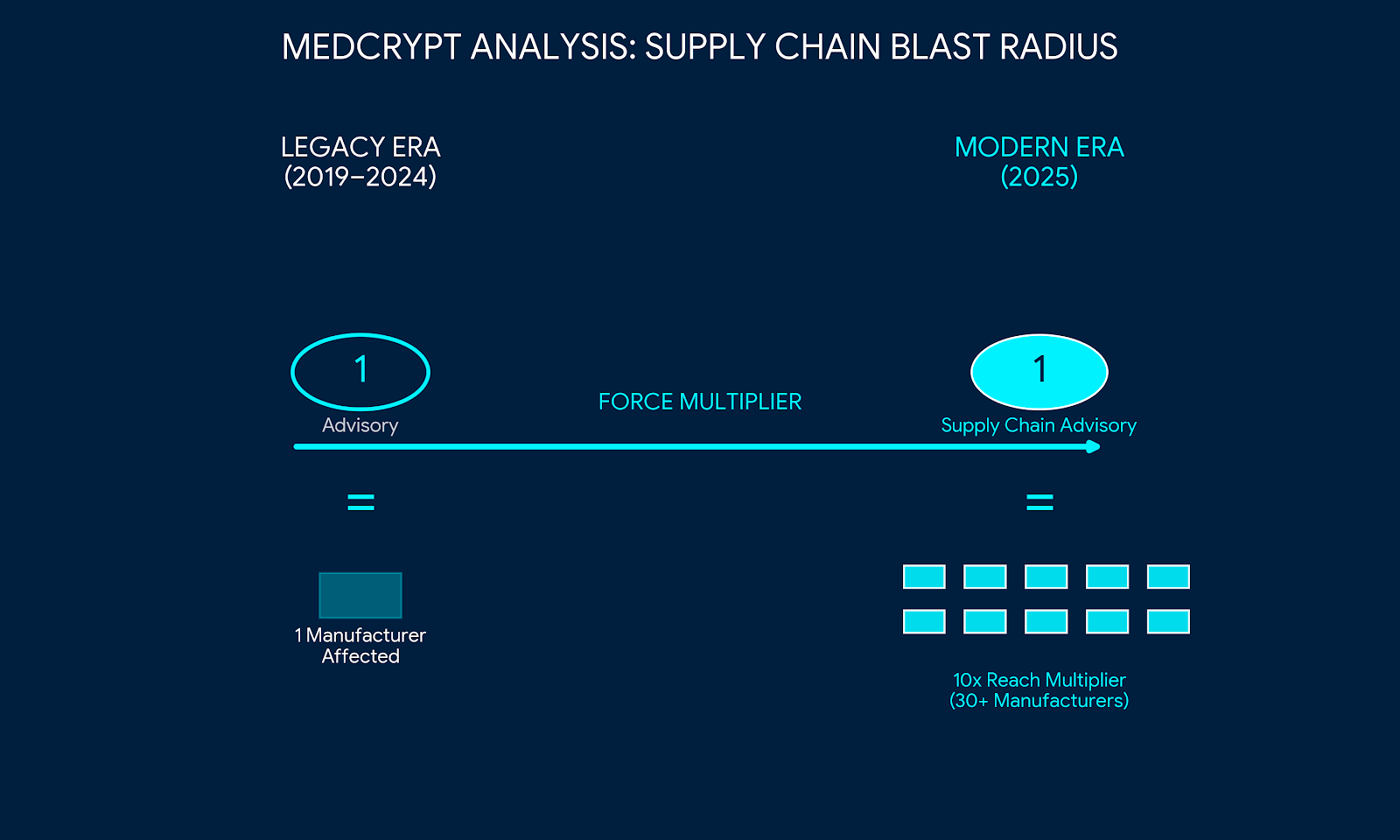
Looking ahead, the risks are moving beyond simple data theft and toward operational paralysis. Any cyber issue—even a minor one—can now trigger a cascade of regulatory findings and fines because of its potential for harm, even if a patient is never actually touched.
The Bottom Line: Regulatory compliance is no longer a "one-and-done" event at the time of clearance. It is a continuous obligation. Financial penalties are being designed to ensure that addressing security isn't just a cost of doing business—it's the only way to stay in business.


April 15, 2026
March 12, 2026

March 4, 2026
Get the latest healthcare cybersecurity news right in your inbox.
We'll never spam you or sell your information

